Are you struggling to protect sensitive data from persistent cyber threats? Learn how modern pattern recognition transforms enterprise security today.
PhantomBlox is a secure data platform that redefines how organizations protect sensitive information. This system converts ingested files into non-human-readable pattern blocks right at the point of entry. The technology removes readable data from persistent storage to render traditional adversarial threat models completely obsolete.
Organizations face constant challenges keeping raw intelligence safe from unauthorized access. PhantomBlox operates on a strict zero-knowledge architecture that treats data as transient patterns rather than static files.
The foundation of this approach is a process called Destroy-on-Load. During ingestion, the system transforms source files into probabilistic representations that contain no intrinsic meaning, file headers, or classification markings.
The original assets are immediately destroyed so no plaintext copy ever persists on the server. This technical transformation effectively collapses the security stack into a single hardened environment.
Companies often conduct AI-readiness assessments to determine how their current infrastructure can support these modern security models. Because a technical breach yields only a database of indistinguishable blocks, the platform removes the primary target for attackers.
AI Readiness and Compliance Assessments
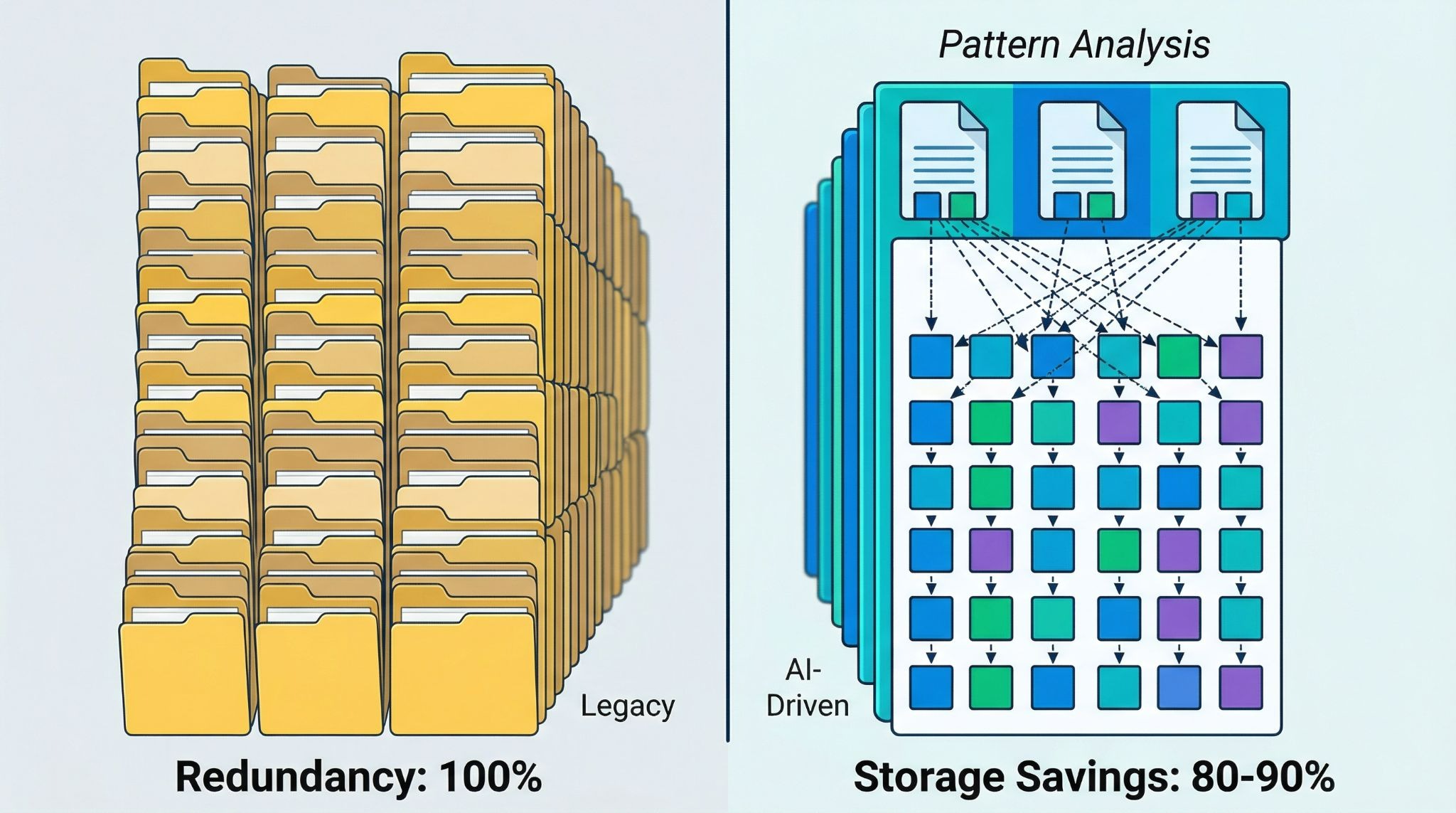
The AI performs deduplication at the semantic and structural level instead of just matching raw bytes. The system learns functional patterns like recurring report templates and metadata fields, much like a child acquiring a basic vocabulary. Once these core patterns are mapped, new documents require no new storage because they are constructed from known elements.
This compounding storage advantage creates a 40 to 70 percent reduction in effective storage requirements within the first two years of operation. The system processes the unique structural makeup of a file, meaning a 10GB file may occupy less than 100MB on the server. This approach to technology innovation and automation allows infrastructure costs to plateau as the platform matures.
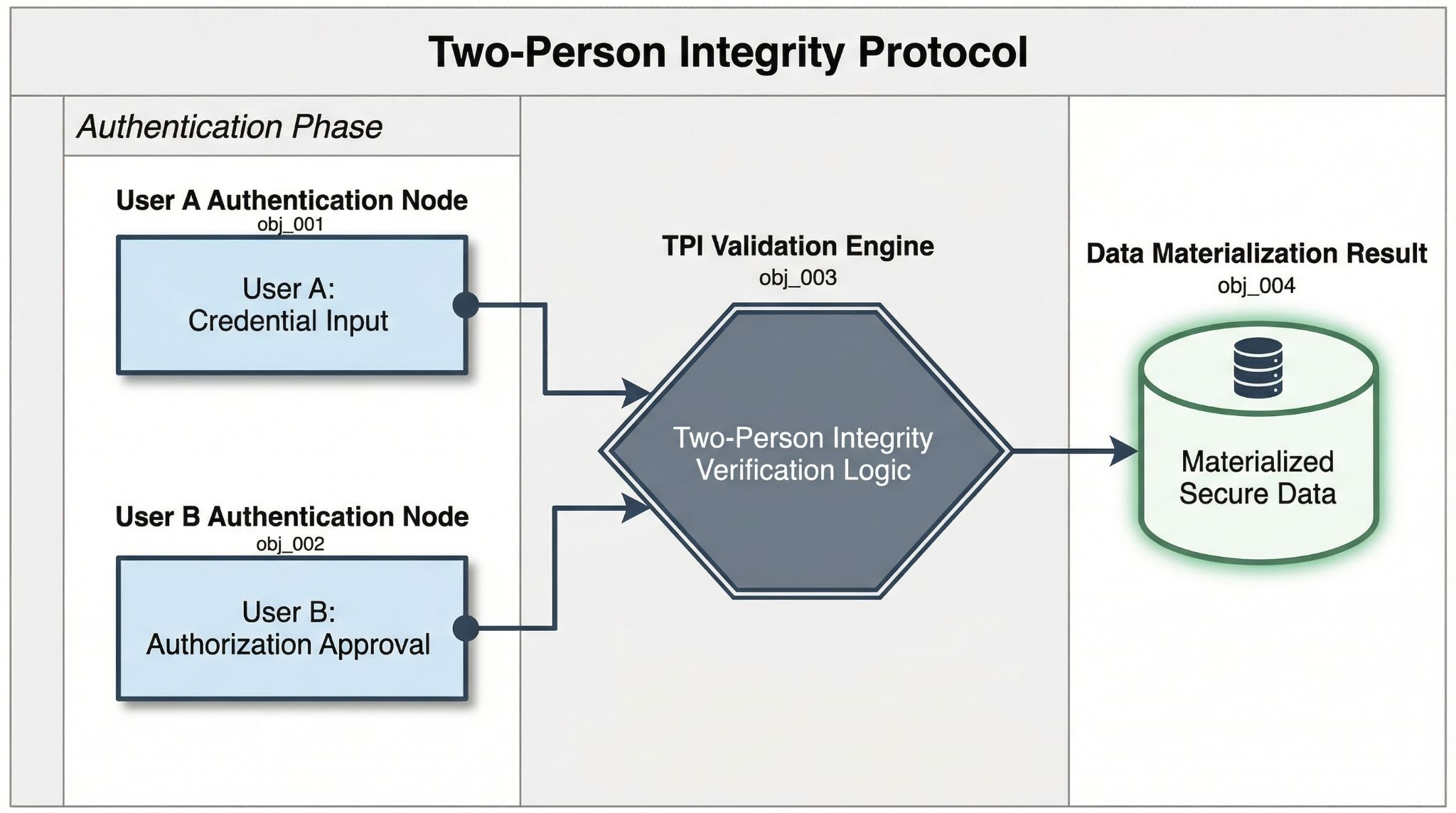
Insider threats require robust access governance built directly into the system architecture. PhantomBlox enforces security through a four-tier Role-Based Access Control model integrated with a Two-Person Integrity protocol. Mirroring nuclear launch doctrine, the reconstruction of any data requires the simultaneous presence and authentication of both Tier 1 holders.
This Dual Key Man system guarantees that no single individual can act alone to reconstruct or download data, regardless of their administrative clearance. Organizations prioritizing security risk management benefit heavily from this rigid verification process. The access keys are revoked instantly upon termination, meaning stored blocks remain permanently meaningless to former employees.
If you want to upgrade your current infrastructure, reach out to Visio Cyber AI to explore secure deployment playbooks and customized strategies.
Transforming pattern blocks back into readable intelligence is a deterministic process requiring six simultaneous conditions to succeed. The absence of a single element results in total reconstruction failure. Both authorized Tier 1 holders must provide independent biometric verification, and the deployment-paired AI model must unlock the reconstruction engine.
The platform then retrieves blocks from the server in a sequence known only to the inference layer. The file is reconstructed with 100 percent deterministic fidelity, meaning no approximation or data loss occurs. Advances in ai data security highlight the value of keeping material out of non-volatile storage. The reconstructed output exists only in volatile memory and is purged immediately after the session.
Technology Innovation and Automation
Historic national security breaches often stem from the persistent storage of human-readable intelligence. PhantomBlox addresses these structural failures by moving to a model where the assumption of data exposure becomes irrelevant. An attacker gaining full server access retrieves only random-looking 512-byte blocks without any filenames or identities to exploit.
The documentation notes that this architecture would have rendered the Manning, Snowden, and Teixeira leaks impossible since the exfiltrated files would have remained unreadable.
The system shifts the focus from querying raw values to identifying and visualizing structural patterns. The integration of ai-driven threat detection further enhances the platform by analyzing model-to-model inference on dedicated hardware.
Large agencies with thousands of users can implement the platform by creating a parallel system. Starting with a Proof of Concept allows the AI node-based solution to run alongside existing operations until management decides to fully switch over. The physical architecture depends on client preference, and servers can be private on-premises hardware or reside within existing cloud environments like AWS or Azure.
Solutions focused on ai-enhanced security offer flexible deployment options for regulated sectors. The system also integrates a native iOS application that technically prevents device-level screenshots to stop physical data theft. To protect against external cameras, hardware-level screens can obscure the view from unauthorized angles.
For more information on aligning your operations with modern compliance standards, schedule an executive education session with the Visio Cyber AI team.
A hacker breaching the access control would find nothing but unreadable patterns. The original files are destroyed upon ingestion, and the system only materializes data once multi-stage approvals are verified.
The protocol is designed for two-party authorization to maintain strict security standards. The system can be configured so that an AI acts as one of the key holders to serve as a backup if a second human is unavailable.
Every step of the approval process is encoded into the system as permanent structural pattern blocks. These are unalterable structural records, which provides much better reliability than traditional text logs that can be edited or deleted.
The system has no size restrictions, removing the data ceiling that often causes legacy tools to crash. It only processes the unique structural makeup of a file to drastically reduce the storage footprint.