Cyber threats are evolving faster than traditional tools can handle. Our Next-Generation, AI-Powered Cybersecurity Platform delivers a unified, intelligent, and adaptive defense tailored to your environment — transforming how organizations detect, analyze, and respond to threats in real time.
Built for both government and commercial environments, this platform combines SIEM, SOAR, and AI analytics within a cloud-native architecture, enabling end-to-end visibility, autonomous monitoring, and scalable threat response — all while reducing operational costs by up to 80%.
CONTACT US.webp)

Consolidate your tech stack into a single, streamlined platform. Replace outdated SIEM and SOAR tools with a solution that unifies log correlation, event orchestration, and AI-driven analytics — eliminating data silos and tool sprawl.

Our agentic and generative AI models continuously learn your environment to detect anomalies, predict threats, and initiate autonomous responses. Real-time remediation reduces mean time to detect (MTTD) and mean time to respond (MTTR) by up to 10x.

Proactively identify hidden risks across petabytes of logs. The platform’s AI copilots and machine reasoning automate Tier 1–2 SOC tasks — empowering analysts to focus on complex investigations and strategic initiatives.

Leverage AI-driven risk scoring, correlation insights, and contextual intelligence to reduce false positives and improve confidence in every security action taken.

Whether deployed on-premises, in hybrid clouds, or across multiple environments, our Cloud-Native Correlation Fabric ensures performance, reliability, and elastic scalability — without compromising security or compliance.

Designed for FedRAMP-aligned and Zero Trust frameworks, our solution simplifies compliance management while maintaining robust data protection and governance controls.
Replace multiple tools with a single, scalable solution.
AI-driven workflows accelerate containment and remediation.
Copilots automate repetitive SOC tasks.
Smarter detection through behavioral and generative AI.
Works with any cloud, endpoint, or data system.
Built to defend against AI-driven threats of tomorrow.
%20(1).webp)
Our AI-Powered Cybersecurity Platform is not just an upgrade — it’s a transformation. It’s a force multiplier for your security operations, empowering teams to move from reactive defense to proactive resilience.
Whether you’re a federal agency securing critical systems or a private enterprise modernizing your SOC, our platform is your strategic ally for the AI era.
CONTACT US
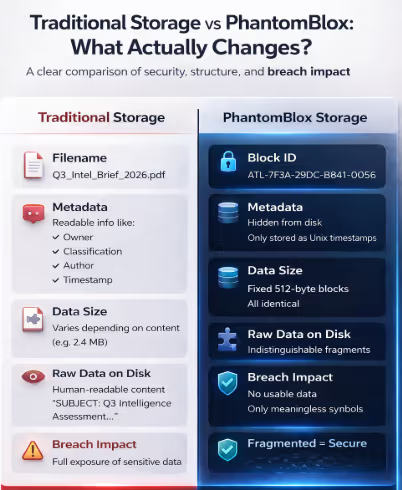
The solution delivers the absolute integration of security, intelligence, and data integrity. By ensuring that human-readable information never resides on the server, PhantomBlox renders the standard adversarial threat model obsolete.
Renders unauthorized server access moot by removing all readable files and metadata from the persistent storage layer.
Implements cryptographic role-based access control (RBAC) and Two-Person Integrity (TPI) protocols, ensuring no single actor can reconstruct data.
Facilitates model-to-model inference on dedicated hardware, eliminating the SIEM aggregation lag inherent in traditional SOC/NOC workflows.
Eliminates the need for multiple and disparate vendor contracts and associated integration labor, collapsing the security stack into a single hardened environment.

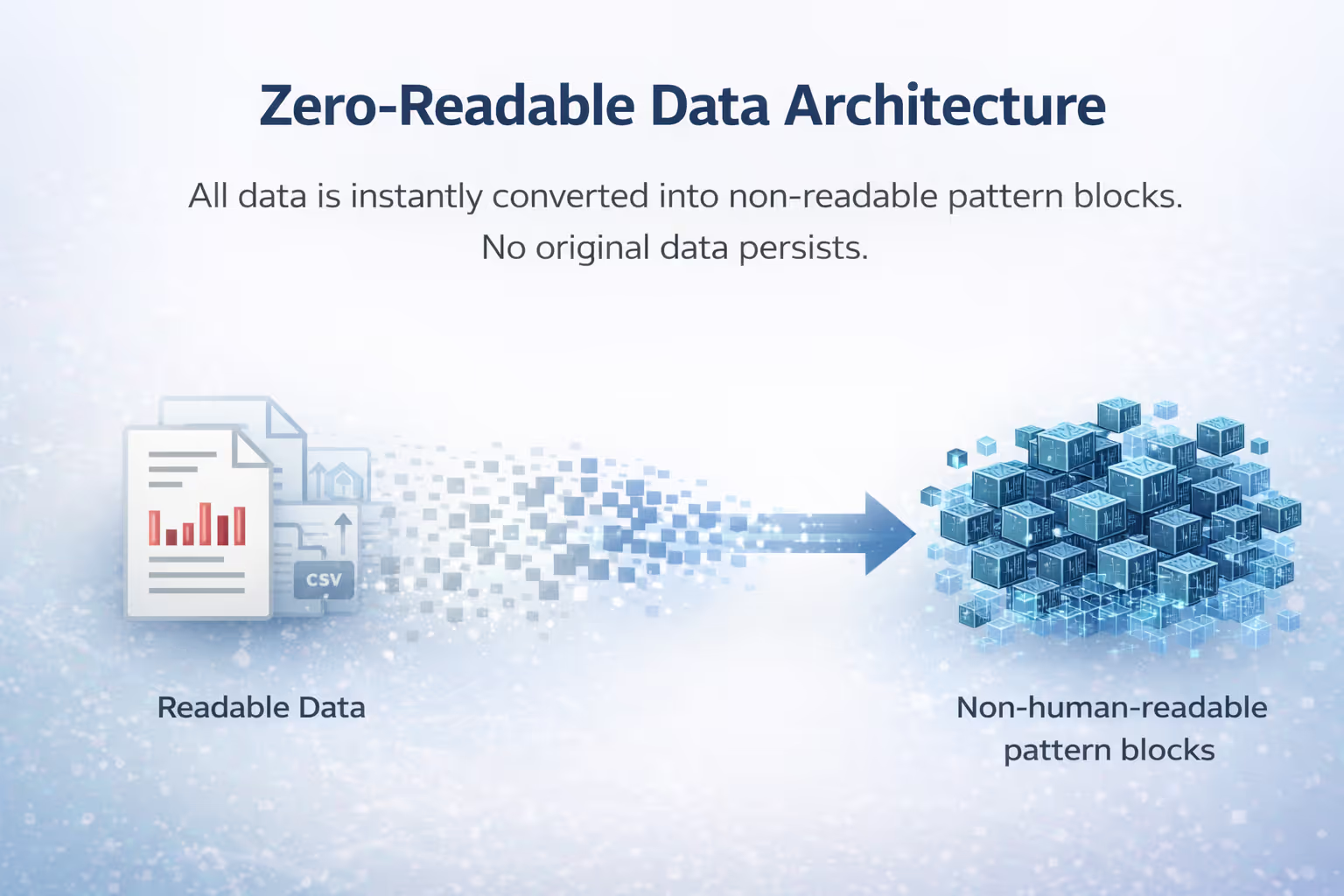
PhantomBlox operates on a zero-knowledge architecture where data is treated as transient patterns rather than static files. This is anchored by the "Destroy-on-Load" mechanism: upon ingestion, source files are immediately processed into 512-byte fixed-size pattern blocks and the original assets are destroyed. No plaintext copy persists on the server. Unlike traditional systems that rely on a third-party SaaS aggregation layer, PhantomBlox utilizes direct model-to-model inference on a hardened, dedicated server.
Core Principles
Source files are transformed into pattern blocks at ingestion; original artifacts are immediately purged from volatile and non-volatile memory.
All reporting and analysis occur via model-to-model inference on a dedicated, hardened node, removing third-party middleware exposure risks.
The ingestion layer transforms data into non-human-readable, 512-byte fixed-size pattern blocks. These are probabilistic representations containing no intrinsic meaning, file headers, or classification markings. A technical breach yields only a database of indistinguishable blocks that cannot be reverse-engineered without the specific paired AI model and simultaneous Dual Key Man authentication.
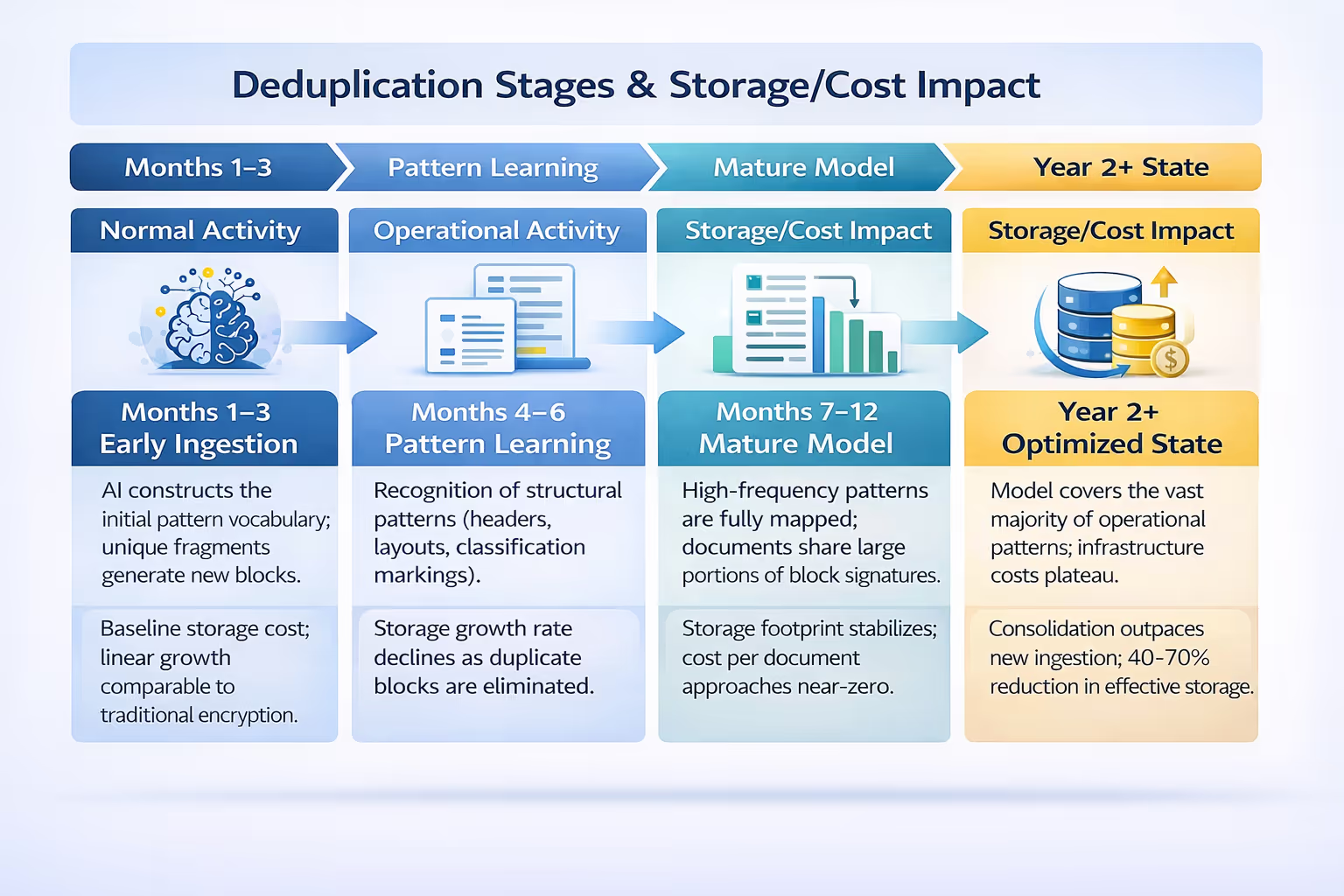
PhantomBlox’s AI performs deduplication at the semantic and structural level. Rather than matching raw bytes, the system recognizes functional patterns—such as recurring report templates, headers, and metadata fields. This is analogous to a child acquiring a vocabulary: once the core patterns of a language are learned, new sentences require no new storage because they are constructed from known elements. This creates a compounding storage advantage where effective requirements are reduced by 40–70% within the first two years of operation.
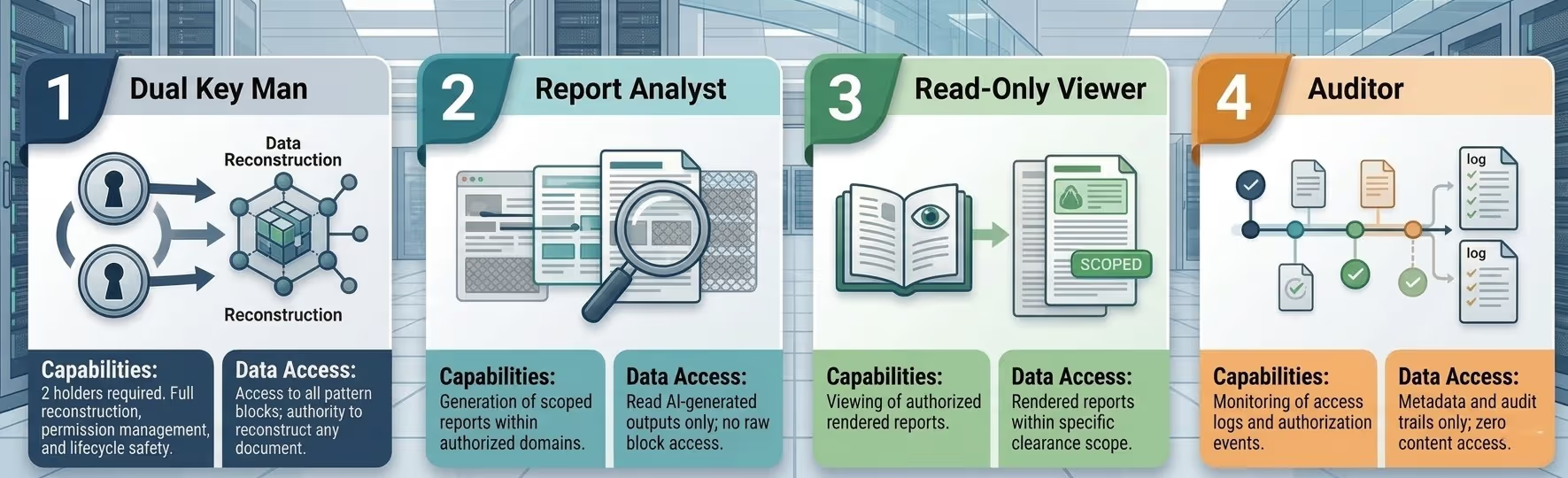
Governance is enforced through a strict four-tier Role-Based Access Control (RBAC) model integrated with a Two-Person Integrity (TPI) protocol. Mirroring nuclear launch doctrine, reconstruction of any data requires the simultaneous presence and authentication of both Tier 1 holders (dual Key Man). Optional AL to serve as a Key Man.

The transformation of pattern blocks back into readable intelligence is a deterministic, verifiable process requiring six simultaneous conditions. The absence of a single element results in total reconstruction failure.
Both authorized Tier 1 holders provide independent biometric verification and credentials simultaneously.
The specific, deployment-paired AI model (not a copy or backup) unlocks the reconstruction engine.
The system retrieves blocks from the server in a sequence known only to the inference layer.
The file is reconstructed with 100% deterministic fidelity; no approximation or data loss occurs.
The report is rendered in a secure session based on the requester’s RBAC tier.
The reconstructed output exists only in volatile memory and is purged after the session; no readable copy is ever written back to disk.
PhantomBlox represents a security revolution that addresses the structural failures behind historic national security breaches. By moving to a zero-readable-data model, the system makes the assumption of data exposure irrelevant.
The Dual Key Man TPI protocol ensures no single person can reconstruct or download sensitive data alone. Access keys are revoked immediately upon termination, and stored blocks remain useless without active TPI authentication.
The AI reconstruction is mathematically consistent, ensuring that every bit of the original document is preserved. This provides military-grade reliability for mission-critical intelligence without the risks of standard plaintext persistence.

The system is built as a native iOS application that technically prevents device-level screenshots. To protect against an individual using an external device (like a smartphone camera) to take a physical photo of the screen, hardware-level screens can be placed over the device to obscure the view from unauthorized angles.
While the protocol is designed for two-party authorization, the system can be configured so that an AI acts as one of the "Key Men" to serve as a backup if a second human is unavailable.
Because the architecture is 100% lossless, every step of the approval process—from managers to security officers—is encoded into the system's "DNA" as permanent, structural pattern blocks. These are not traditional text logs that can be edited or deleted; they are unalterable structural records.
? In traditional systems, a breach of the RBAC often exposes the "honey pot" of data it protects. In this architecture, the original files are destroyed upon ingestion and converted into pattern blocks. A hacker breaching the access control would find nothing but unreadable patterns because the system only “materializes” data once multi-stage approvals are verified.
The system shifts the focus from querying raw values to identifying and visualizing structural patterns. It visualizes the relationships and repetitions between pattern blocks, allowing users to see trends and anomalies across massive datasets without ever exposing sensitive, raw source data.
Yes, the system is 100% lossless, ensuring that any visualizations or reconstructed reports are perfectly accurate representations of the original input. This differs from traditional compression algorithms, which often lose bits of data.
The recommended approach is to create a parallel system, starting with a Proof of Concept, that runs alongside existing operations until management decides to fully switch over. The system is AI node-based and can be as large as the environment it is required to handle.
The physical architecture depends on the client's preference. The servers can be private, on-premises hardware, or they can reside within existing cloud environments like AWS or Azure.